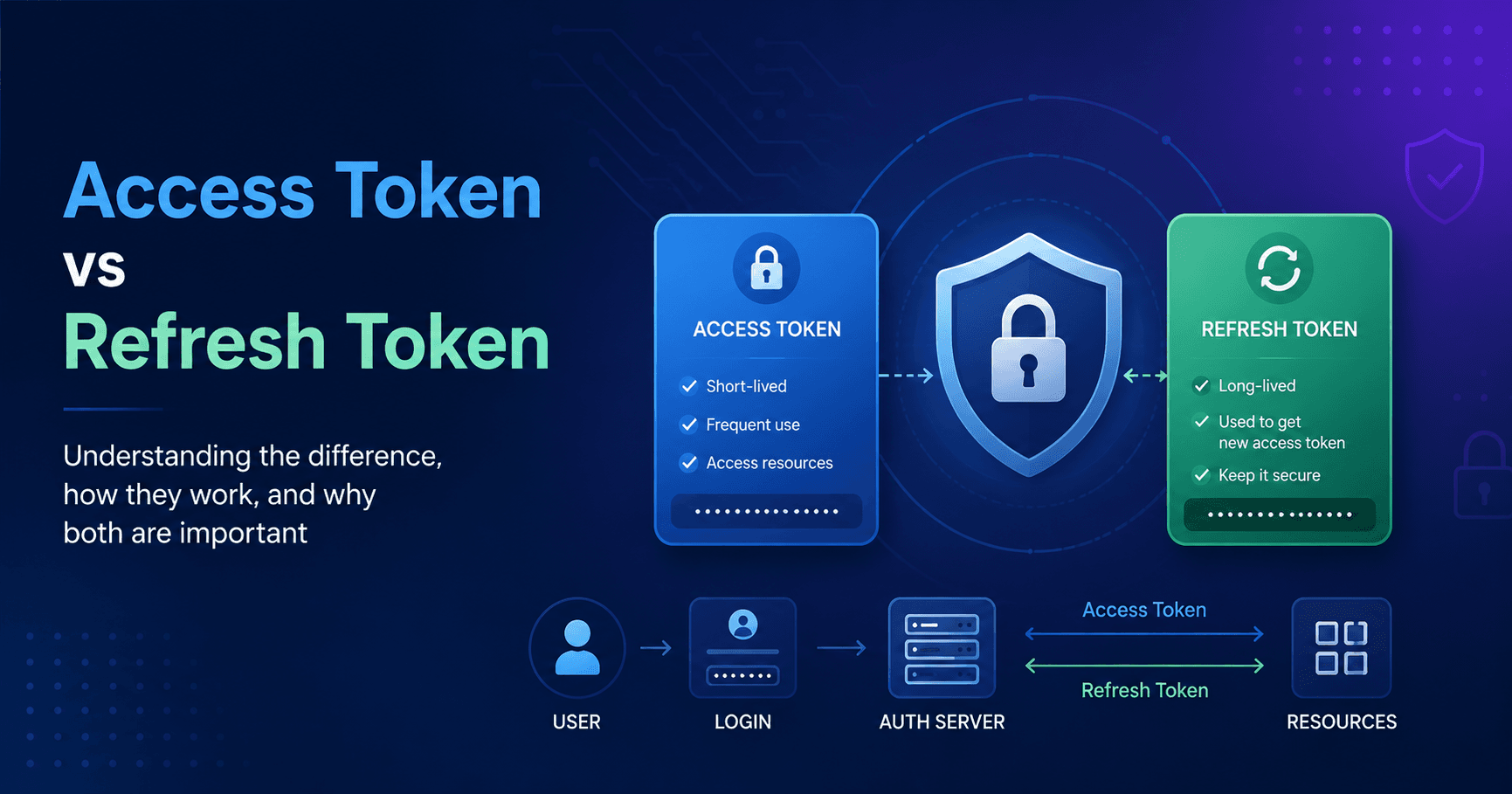
JWT Authentication: Access Token and Refresh Token Flow Explained
In today's interconnected digital landscape, secure and seamless user authentication is paramount. Behind every successful login and persistent session lies a sophisticated interplay of cryptographic
May 16, 20264 min read1

