JWT Authentication: Access Token and Refresh Token Flow Explained
In today's interconnected digital landscape, secure and seamless user authentication is paramount. Behind every successful login and persistent session lies a sophisticated interplay of cryptographic tokens. Among these, Access Tokens and Refresh Tokens stand out as a fundamental duo, working in tandem to provide both robust security and an uninterrupted user experience. This article will demystify these tokens, explain their individual roles, their collaborative flow in JWT authentication, and why they are indispensable in modern applications.
1. Access Token vs. Refresh Token: A Simple Analogy
To grasp the core concept, let's use a simple analogy:
imagine you're attending an exclusive , members-only club.
Access Token (The Club Pass): When you successfully show your membership at the door, you're given a special club pass. This pass grants you immediate entry and allows you to access all the club's amenities (e.g., the bar, the lounge, the dance floor). It's incredibly convenient for quick access. However, for security reasons, this pass is only valid for a very limited time – perhaps just for that evening, or even a couple of hours. If you try to use an expired pass, you'll be denied entry.
Refresh Token (The Secret Membership Key): Along with your club pass, you also possess a more powerful, secret membership key. This key doesn't get you into the club directly. Instead, if your club pass expires while you're still inside, or if you leave and want to re-enter later without going through the full membership verification process again, you can present this secret key to the club manager. The manager verifies your secret key and, if it's valid, issues you a brand new club pass. This secret key is designed to be much longer-lived than the club pass, allowing you to maintain your "membership" without constantly re-verifying your identity from scratch.
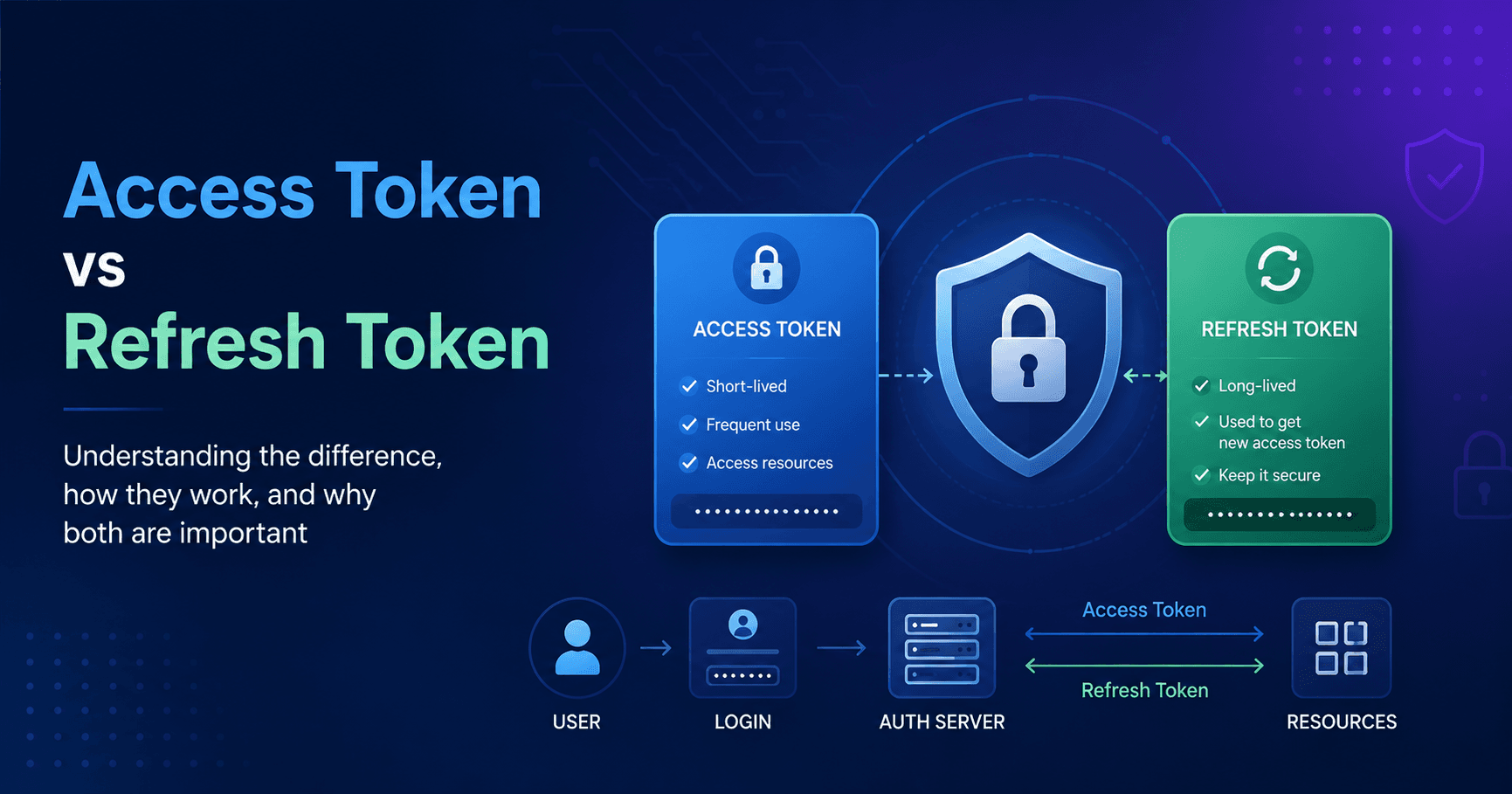
This illustrates the fundamental difference: the access token is your short-term credential for resource access, while the refresh token is your long-term credential for obtaining new access tokens.

- JWT Authentication: Access Token and Refresh Token Flow Explained
When you log into an application using JWT (JSON Web Token) authentication, here's how the access token and refresh token typically work together:
Login: You enter your username and password. The server verifies your credentials.
Token Issuance: If successful, the server issues two tokens: an access token (short-lived) and a refresh token (long-lived).
Access Resource: Your application uses the access token to make requests to protected resources (e.g., fetching your profile data). The server checks if the access token is valid and not expired.
Access Token Expiration: After a short period, the access token expires. Any subsequent requests with this expired token will be rejected by the server.
Token Refresh: Instead of asking you to log in again, your application sends the refresh token to a special endpoint on the server.
New Access Token: If the refresh token is valid, the server issues a brand new access token (and sometimes a new refresh token too, depending on the implementation).
Continue Session: Your application now uses the new access token to continue making requests without interruption.
Conclusion: The Backbone of Modern Session Management
The strategic implementation of access tokens and refresh tokens forms the backbone of secure and efficient session management in contemporary web and mobile applications. By combining the immediate utility and short lifespan of access tokens with the long-term, behind-the-scenes power of refresh tokens, developers achieve a critical balance: they enhance security by limiting the exposure of sensitive credentials, while simultaneously providing users with a fluid, uninterrupted experience that avoids constant re-authentication.
For professionals like myself, Dhanraj Sahu, a Master's degree understanding these intricate authentication flows is not merely academic; it's a fundamental requirement for designing and implementing robust, scalable, and secure systems. As applications grow in complexity and user expectations for seamless interaction rise, mastering the nuances of token-based authentication, particularly the access token and refresh token paradigm, remains an indispensable skill. It ensures that the digital experiences we build are not only functional and user-friendly but also resilient against the ever-evolving landscape of cyber threats.

